GPU Mining &
Blockchain Mechanics
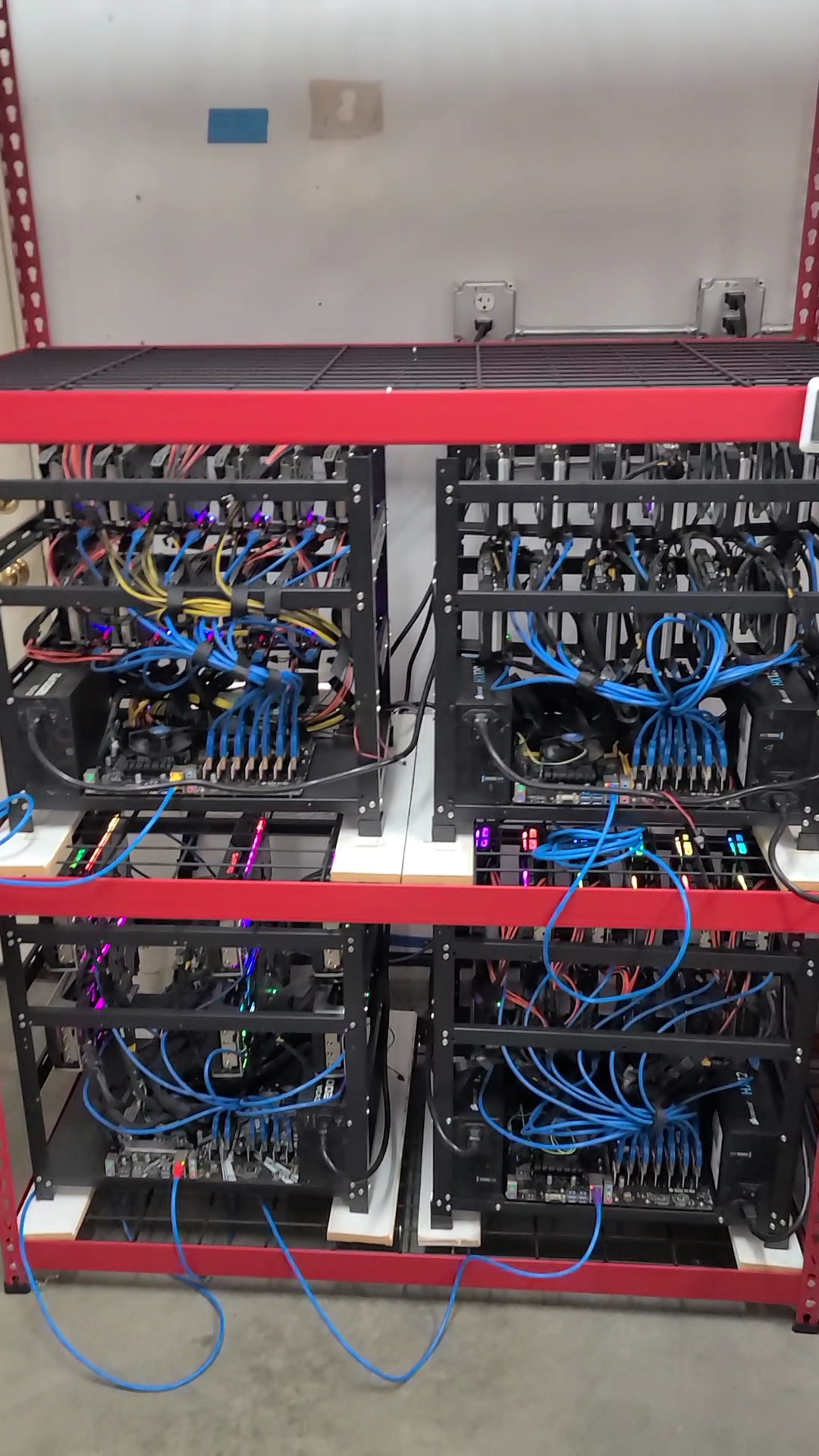
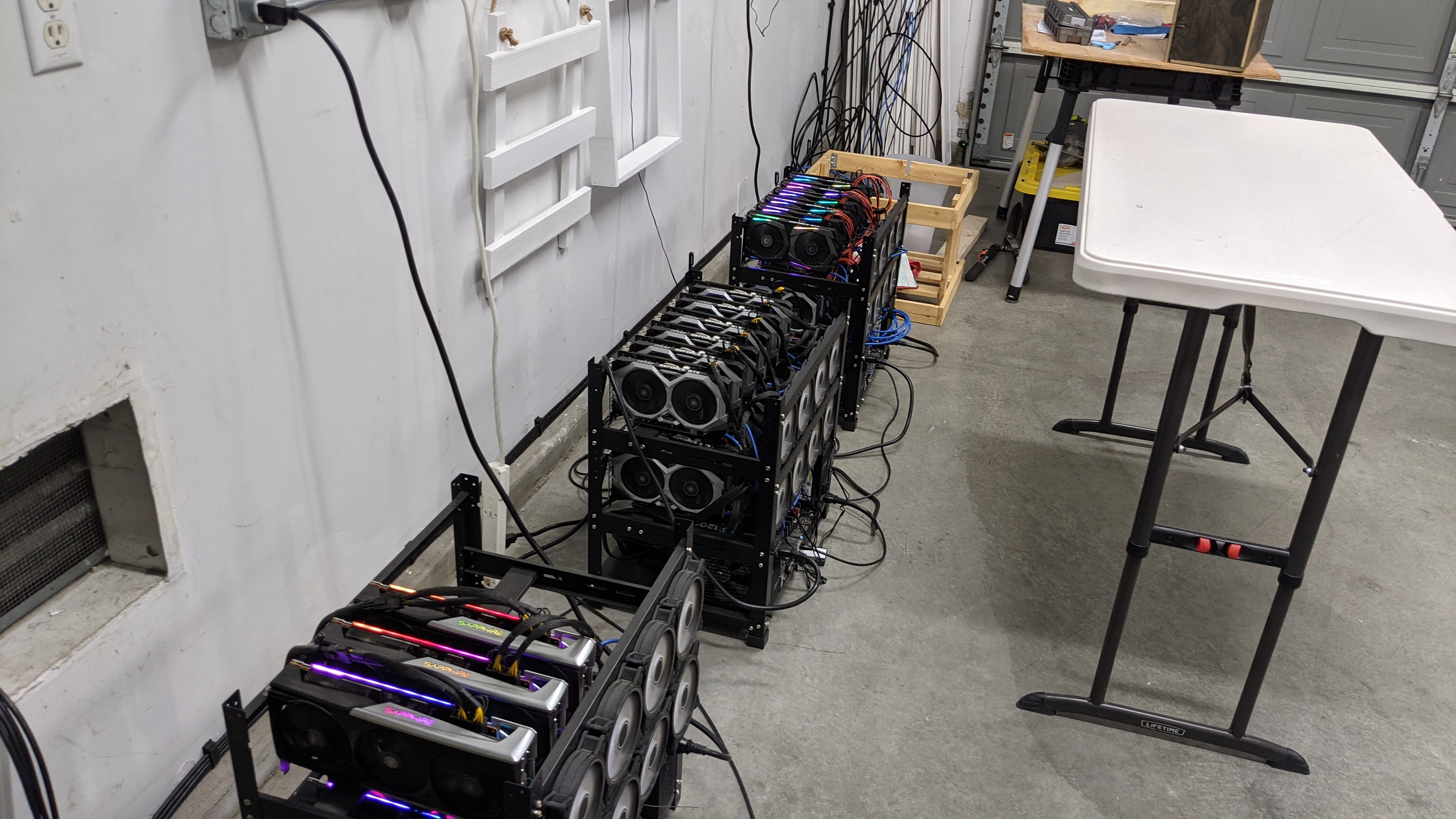
This project scaled from a single rig to six at its peak in my garage. It involved custom woodframe built to aluminum rigs, garage HVAC planning to manage thermal load, and deep dive network analysis using Wireshark.
Blockchain Fundamentals
What is Cryptocurrency?
Cryptocurrency is digital money powered by blockchain. A secure, public ledger verified by a global network of nodes. Managed by this network instead of a central authority, it facilitates decentralized transactions.
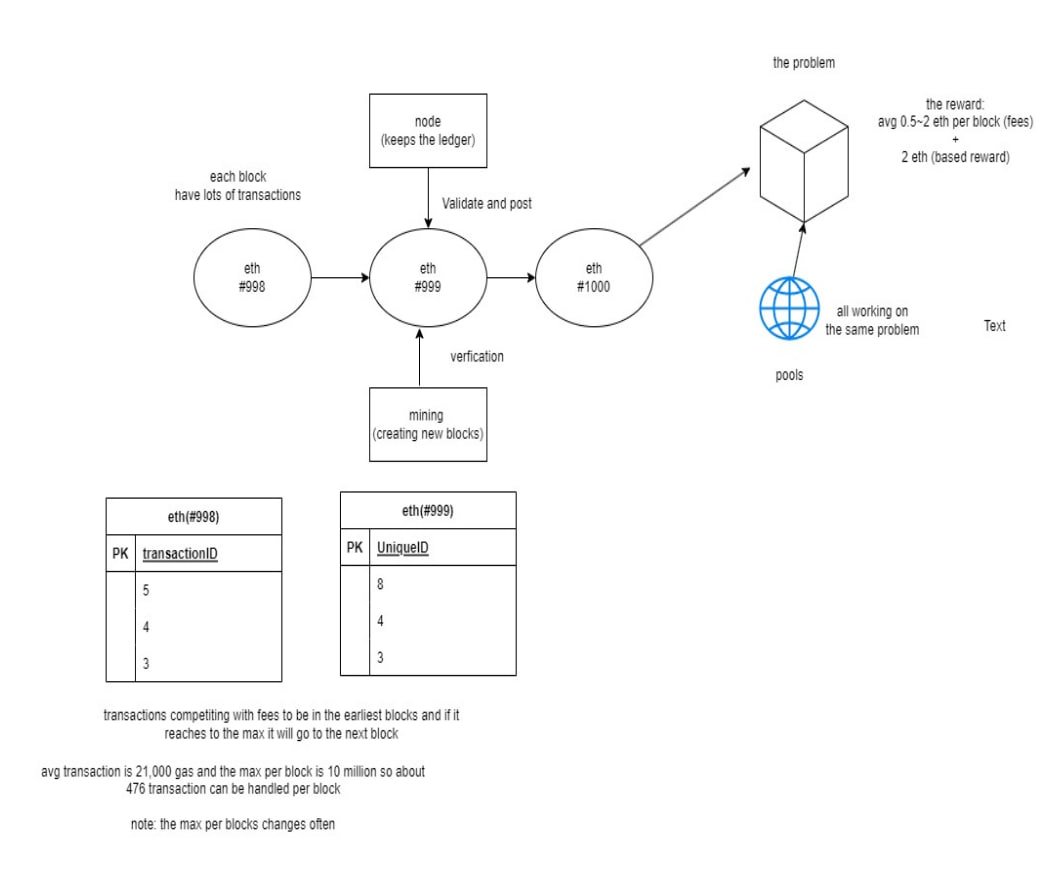
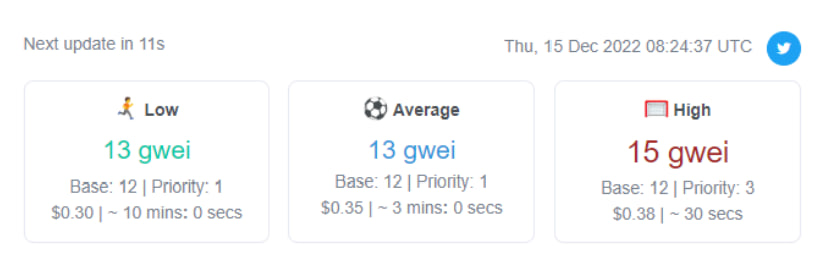
Mining solves complex computational problems under a Proof of Work (POW) model. Miners validate transactions and create new blocks to earn rewards, which fluctuate based on difficulty and sender priority bids.
Fee Calculation (Alice to Bob)
Total Fee = gwei * (gas + tip)
100 gwei * 21,000 gas = 2.1M gwei
Conversion: 2,100,000 gwei = 0.0021 ETH
Total Fee (@$2000/ETH): $4.20 USD
Alice sends 1.0021 ETH; Bob receives 1 ETH.
System Use Case Analysis
Before physical deployment, I mapped out the system interactions. These diagrams illustrate the relationship between the Miner (User), the Mining Client (Software), and the Blockchain Network (External System).
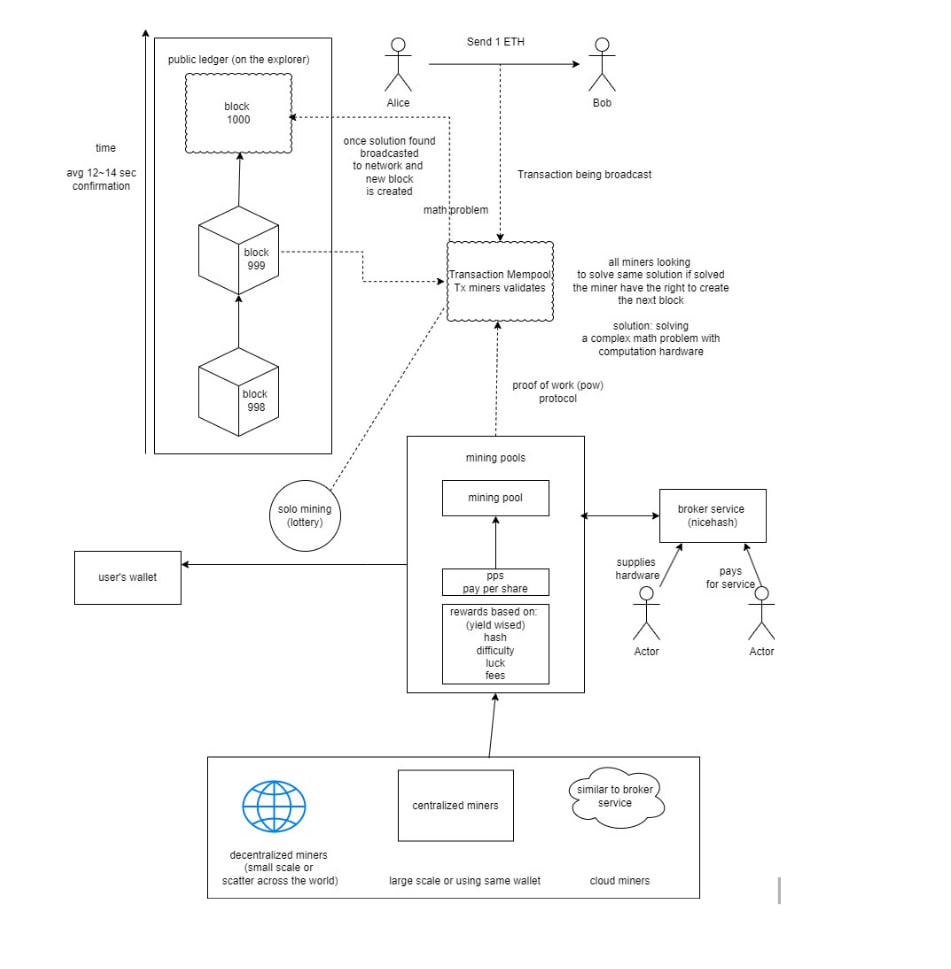
Interaction Model A: User to Local Client
Interaction Model B: Client to Network Pool
Hardware & Software Requirements
Compute & Storage
- CPU: LGA1151 socket type (basic/cost-effective).
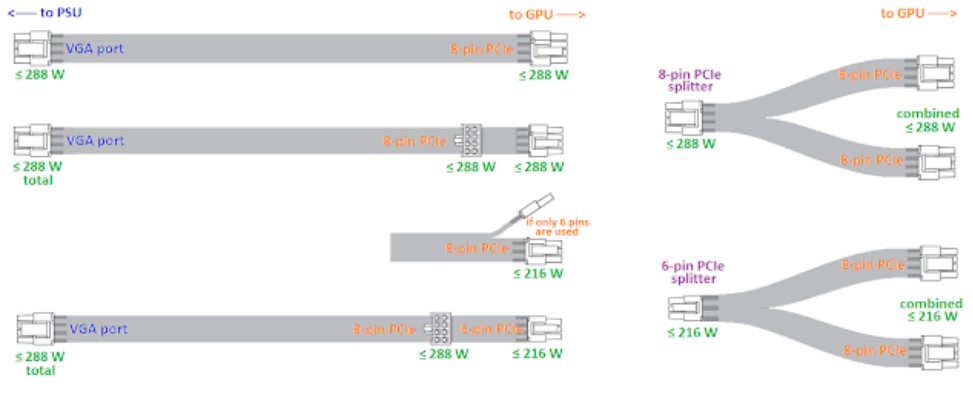
- Motherboard: PCIe slots with riser support or PCI Splitters.
- RAM: 4GB is sufficient.
- Storage: 128GB (Windows) or 64GB (Linux) SSD.
Mining Infrastructure
- GPU: Verified by DAG size calculator (>4GB recommended).
- Risers: PCIe risers for external seating.
- Frame: Open-air structure for ventilation.
- OS: HiveOS or SimpleMining for remote management.
Connectivity & Safety
- Cables: VGA/PCIe cables only. Discard SATA for risers.
- Network: Hardwired Ethernet (Avoid wifi).
- Power Switch: Physical toggle to boot the system.
The 80% Rule
To ensure efficiency and safety, avoid exceeding 80% of the PSU's rated capacity for 24/7 loads. Always calculate from Max TDP to account for software spikes.
Example:
Six 1660 Ti GPUs (120W TDP each) = 720W. Aim for a 1000W PSU.Server PSU & Breakouts
Server PSUs are cost-effective for continuous operation. When using breakout boards (e.g., X11 AMP or ZSX), ensure enough PCIe connectors are available for GPUs and risers.
Step-by-Step & Maintenance
Deployment Workflow
- 1 Currency: Research PoW/PoS census models.
- 2 Wallet: Create and record your unique address.
- 3 Assemble: Map power draw inputs/outputs carefully.
- 4 Miner: T-Rex (Nvidia) or TeamRedMiner (AMD).
- 5 Configuration: Update wallet address in .bat files.
- 6 Optimization: Test stable overclocks via community data.
Troubleshooting & Stability
- BIOS: Enable "Above 4G Decoding".
- Fans: Baseline 80% speed for chip longevity.
- Extra Risers: Keep spares; clean if detection fails.
- 20-Min Check: Run rig for 20 mins before leaving unattended.
- Safety: Verify wall outlet condition and 80% power rule.
Thermal Controls
Ensure at least one GPU's width of space between cards. Proper intake and outtake prevent overheating.
Hardware Care
Use air blower regularly; hold GPU firmly while cleaning. Replace thermal pads if VRAM exceeds 90°C.
Windows (Not Recommended)
Match virtual memory to GPU count + VRAM (e.g., 36GB for 6x 1660 Ti). Disable updates and use auto-start scripts.
Project Deployment Phases

Phase 1: Setup

Phase 2: Configuration
Phase 3: Deployment
Mining Pool & Network Analysis
1. Strategic Pool Selection
Choosing a pool involves balancing geographic proximity to minimize stale shares and evaluating fee structures. Higher priority gas fees (gwei) ensure faster transaction confirmation on the blockchain.
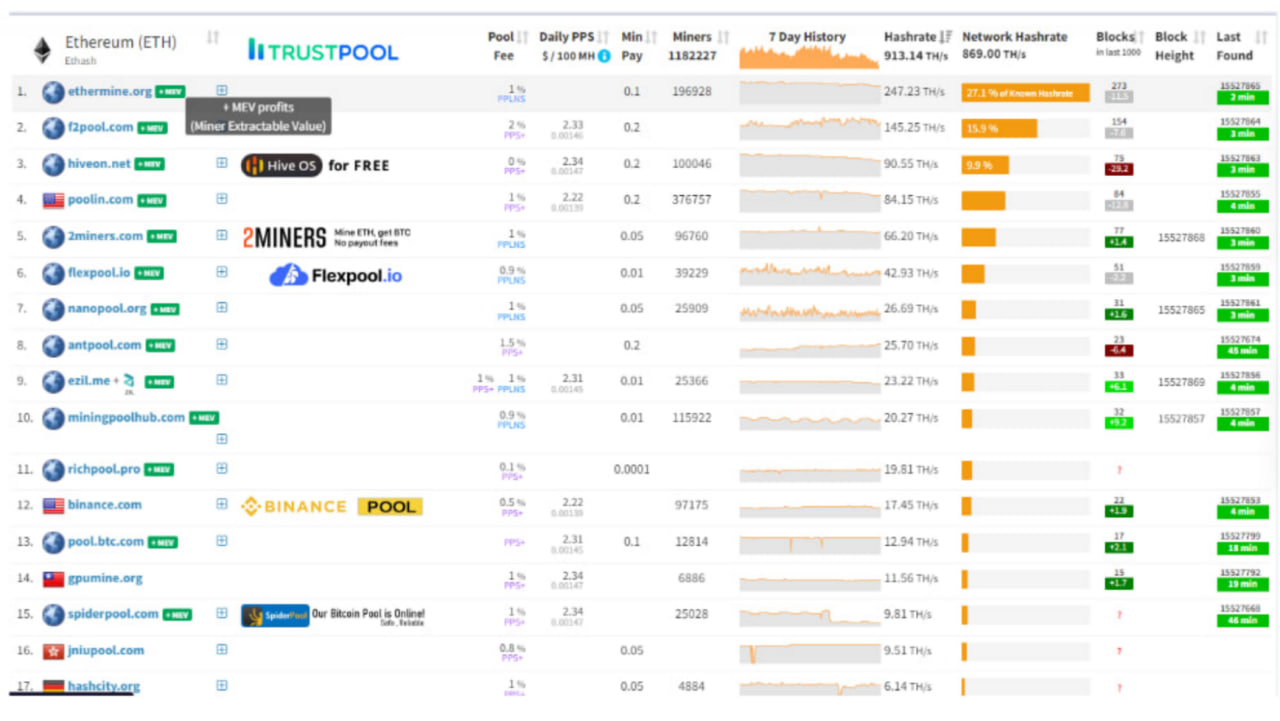
2. Gas Fee Analysis
Real-time monitoring of base vs. priority fees is essential for calculating net profitability, especially during periods of high network congestion.
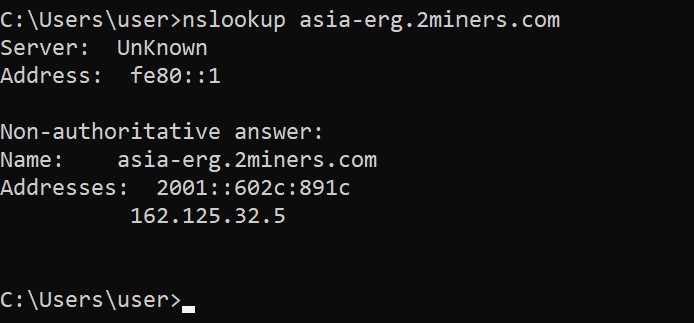
3. DNS Resolution (nslookup)
Verifying the pool's IP address (162.125.32.5) via DNS ensures the miner is connecting to the correct endpoint rather than a hijacked or stale record.
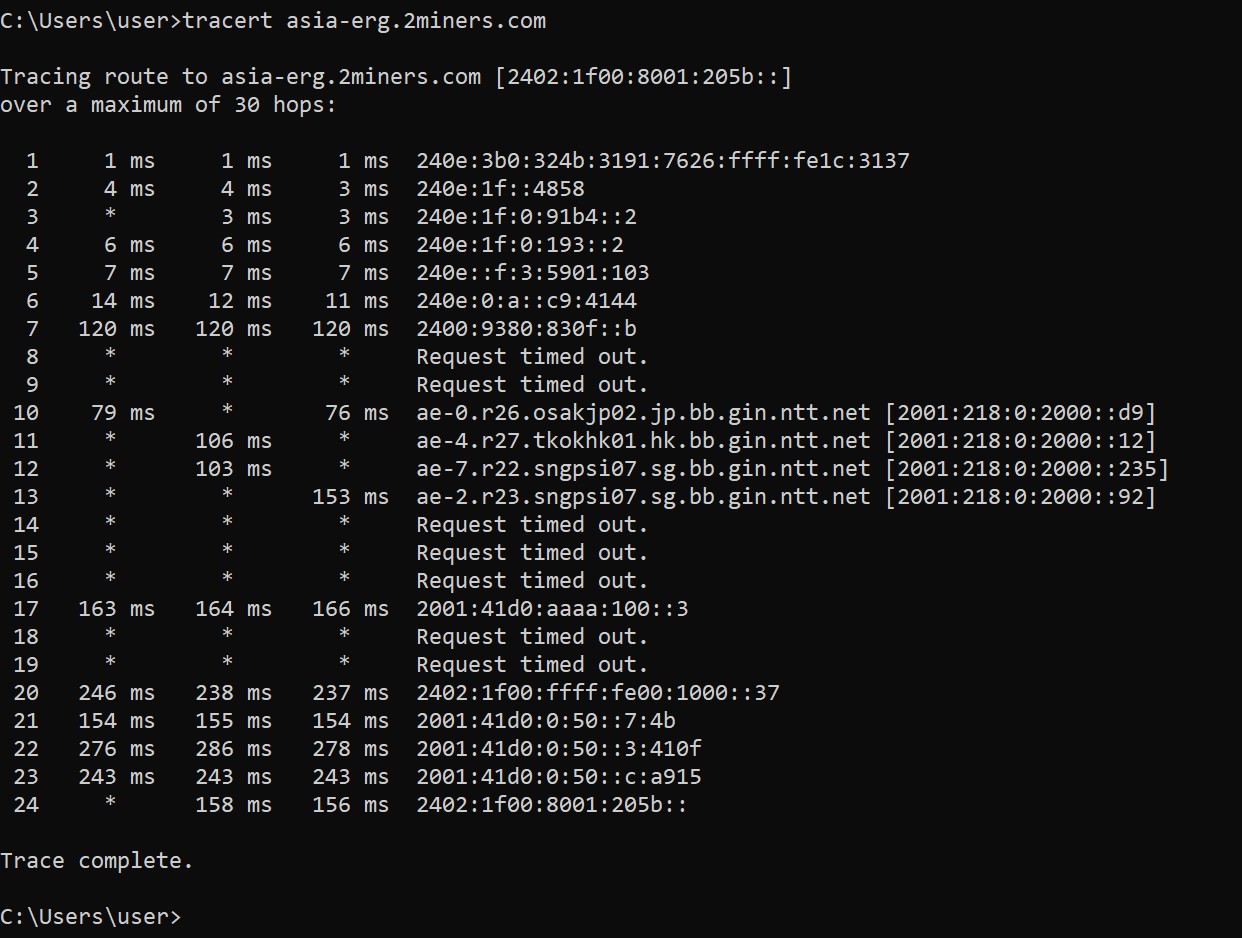
4. Path Latency (tracert)
Analyzing the "hops" to the destination reveals where latency spikes occur. Maintaining low ms response times is critical for competitive PoW mining.
Wireshark Traffic Analysis
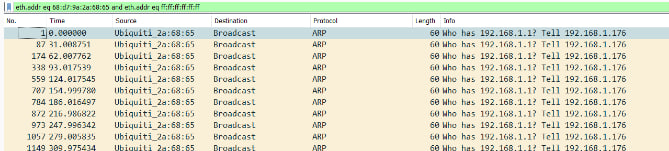
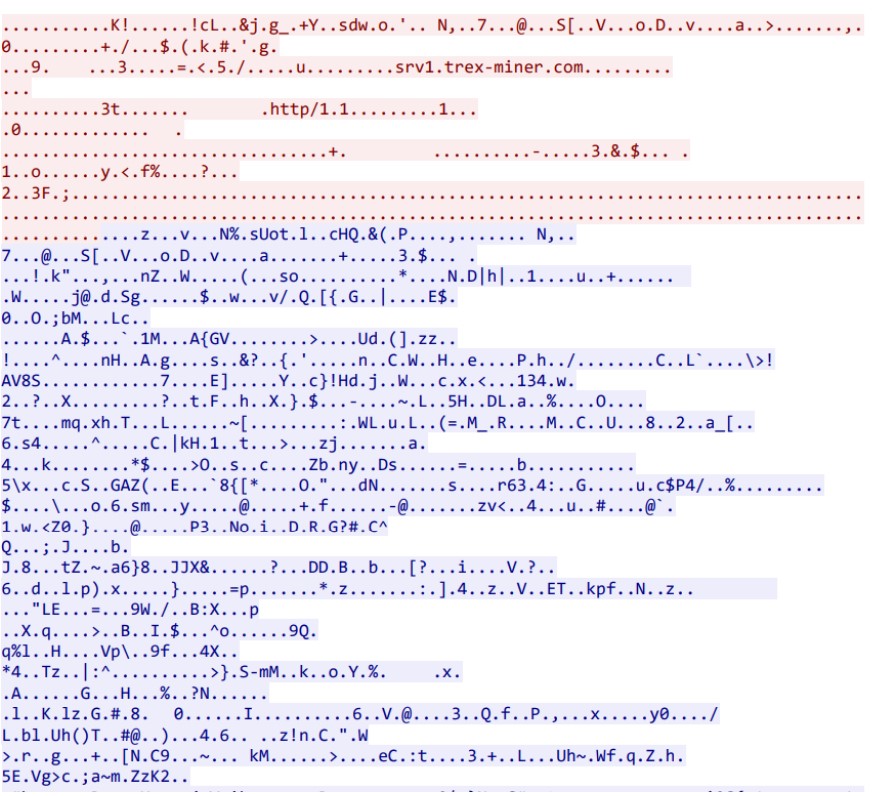
Network Traffic & Capture Properties
Initial data capture was performed to establish a baseline for rig-to-pool communication. The capture file properties confirm the hardware interface used and the total packet count over the observation period.
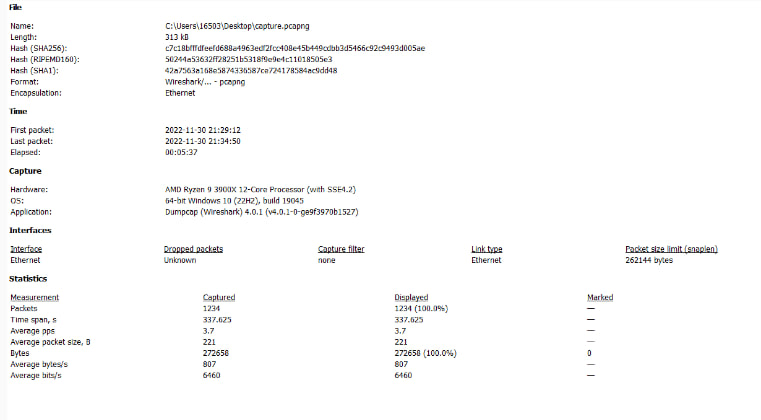
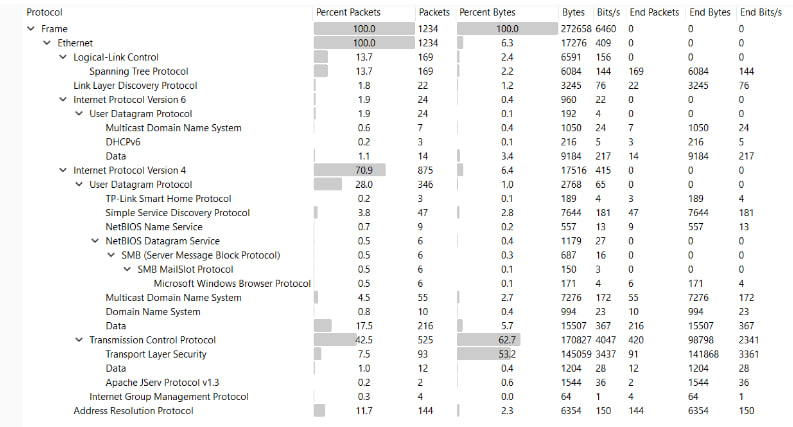
Protocol Hierarchy
By analyzing the protocol hierarchy, I confirmed that IPv4 is the dominant protocol. UDP handles low-latency DNS requests, while TCP manages the reliable delivery of mining shares.
Conversations & Endpoints
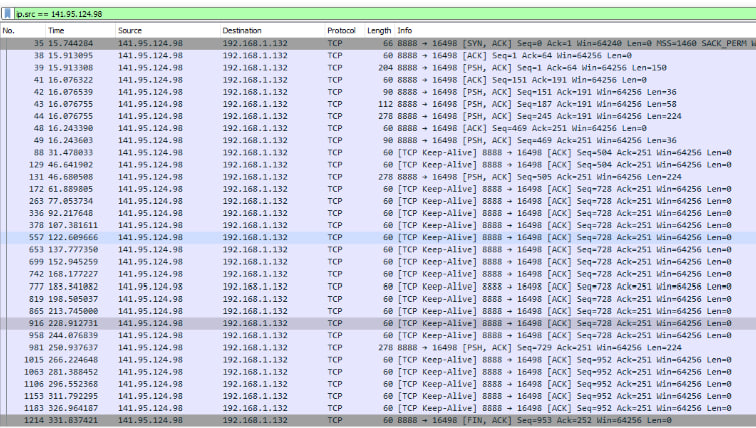
Mapping endpoints allowed me to isolate the mining rig's local IP and verify its direct communication path with the pool's server. The conversation statistics show the total bytes exchanged, confirming steady-state data transfer.
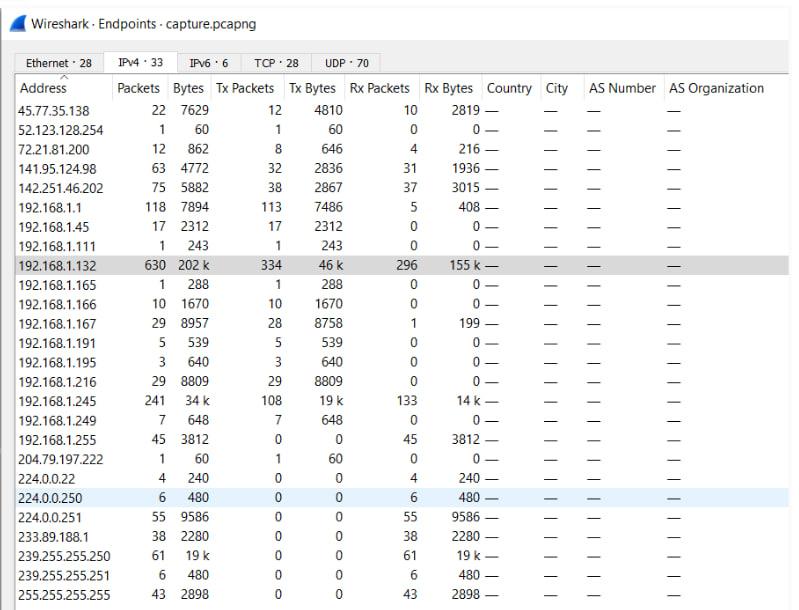
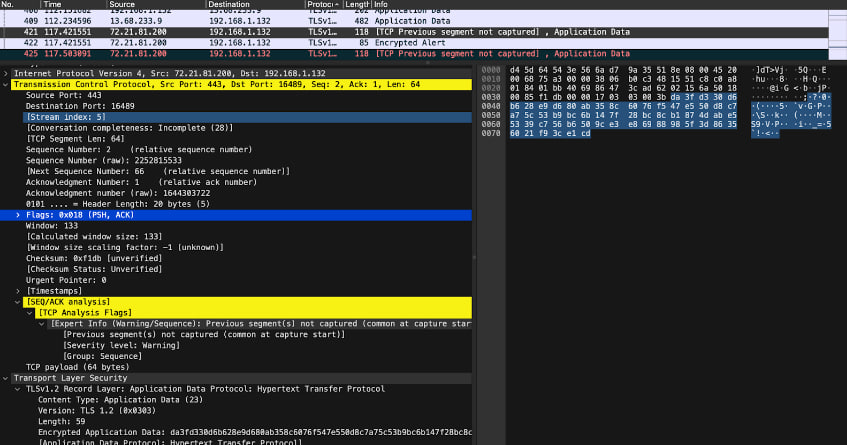
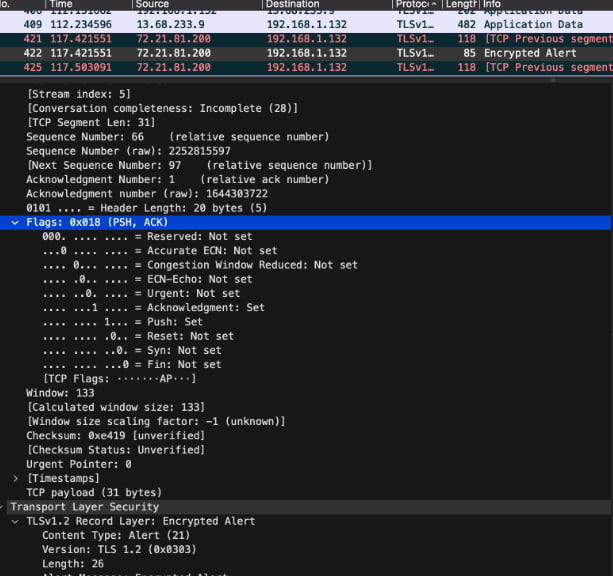
Evidence of Security & Scenario
"Analysis of communication between the miner (192.168.1.132) and the pool (141.95.124.98) confirms the traffic is encrypted via TLS."
Scenario Analysis:
Verified that the Stratum protocol over TLS prevents 'man-in-the-middle' share hijacking.
Summary
In conclusion, this experience taught me far more than traditional learning from an instruction book. I had to search various resources, like Bitcointalk, Reddit, YouTube, and Discord, to solve issues I encountered over the years.
This was my first project scaling up from a single rig to six rigs at its peak in my garage, which eventually required a dedicated space for the mining setup. I hadn’t anticipated needing to do additional hands-on work, like building a rig frame from wood, installing an exhaust fan in the garage, setting up multiple electrical outlets, and modifying the garage door to improve airflow by bringing in outside air. I also had to learn the basics of data center HVAC principles to manage temperature and airflow effectively in this unconventional environment.
I was also curious how data runs through the network, mining pools, and the blockchain. I was able to identify the network communication happening throughout the capture with the use of Wireshark. With the help of Wireshark, I was able to find the protocols, conversations, endpoints, and lastly, identify the security aspect—ensuring that communication was encrypted.